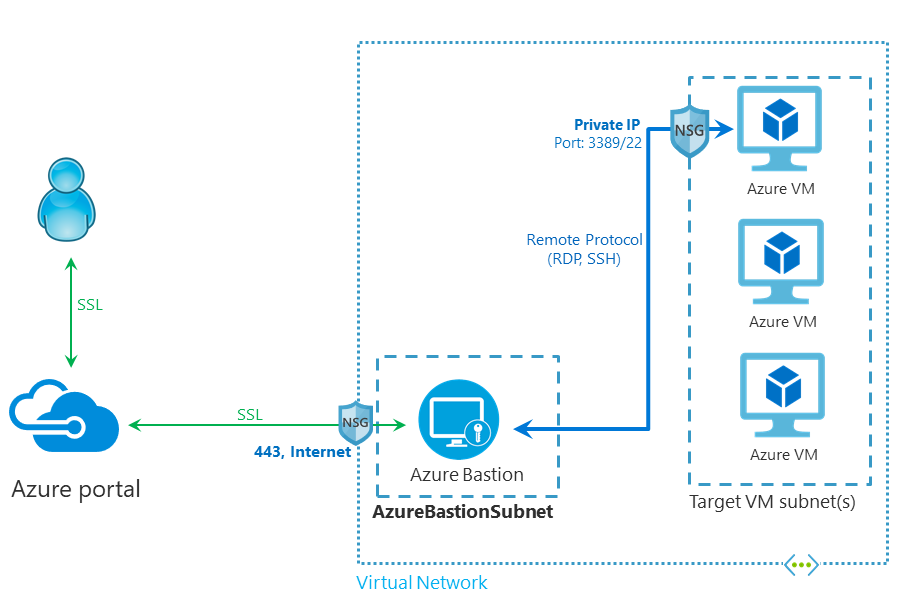
You might be using Public IP, VPN or a Jumpbox to get into Azure Virtual Machines. What if you can get into an Azure VM from within the Azure Portal? That’s what exactly Azure Bastion allows you to do.
Azure Bastion is fully managed PaaS service which provides secure RDP and SSH access to your virtual machine in Azure directly through Azure Portal. It secures your strategic and critical assets in order to protect you from cyber risks. It is the only node exposed to the internet, and it is acting as a Gateway.
You can deploy and use the Bastion resource in any of these regions mentioned below, this may change in future as Microsoft will rollout this service to other regions.
- West US
- East US
- West Europe
- South Central US
- Australia East
- Japan East
Pre-Requisites
To create an Azure Bastion, you must create a Virtual Network with Subnet name as AzureBastionSubnet and with the prefix of at least /27.
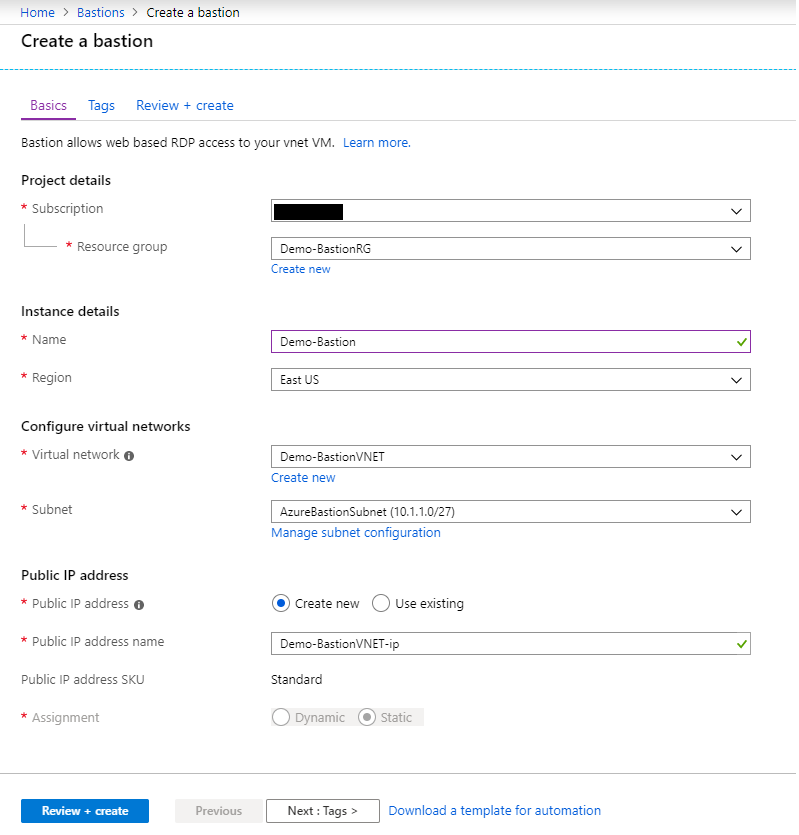
Deployment for Azure Bastion
- Open the Azure Portal.
- Once you are in Azure Portal go to Create Resources and search for Azure Bastion.
- Specify the configuration settings for your Bastion resource:
- Select a Resource Group
- Enter the name.
- Select the region
- Select a Virtual Network
- Select the Subnet you created earlier.
- Select a Public IP Address
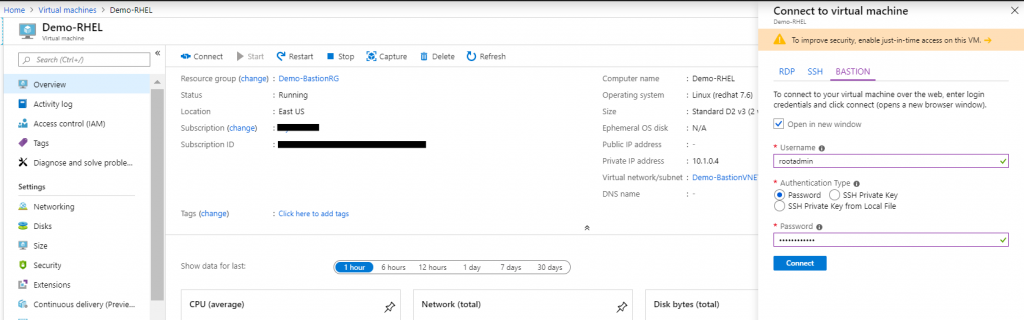
Connect to a virtual machine
Now if you click Connect, you can see a new option called Bastion. You can then type the admin credentials for the virtual machine and click Connect.
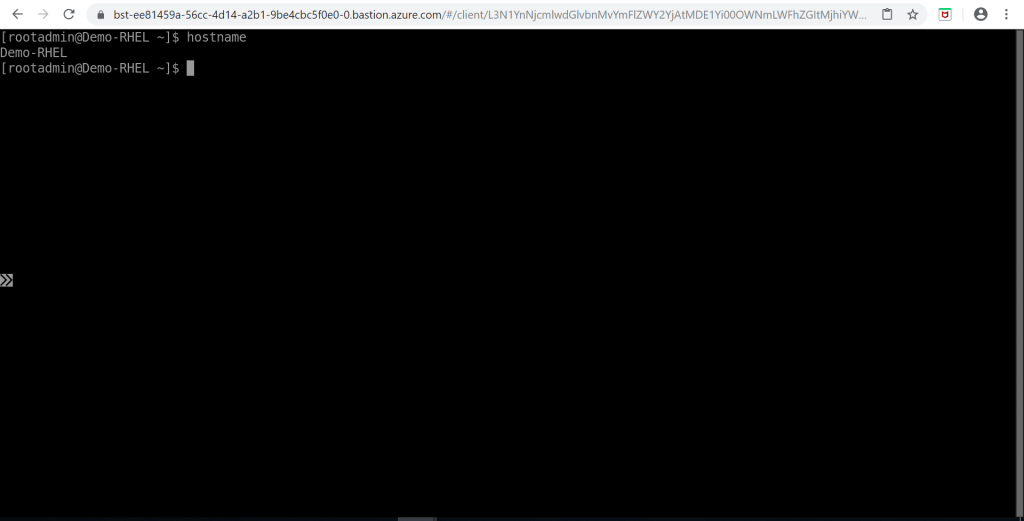
A new browser tab opens, with Bash as its the Linux VM.
For additional reference, check the documentation.
Interested in Microsoft Azure, Let’s CONNECT!







